This reference lists every resource, action, constraint, and field in the MX8 Labs permissions system. Use it alongside the Understanding Roles and Permissions overview and the Managing Roles and Permissions how-to guide.
Resources
Resources are the objects that permissions are applied to. The wildcard resource (*) matches all resources and is used to grant blanket access — for example, read access to everything in the account.
| Resource | Description |
|---|---|
* (All Resources) | Wildcard that matches every resource. Typically used for broad read access. |
account | The account record — name, data residency region, and retention settings. |
account_asset | Shared files, images, and other assets uploaded to the account. |
exposure_source | Ad exposure tracking integrations for linking advertising data to respondents. |
project | A container that groups related surveys for shared reporting and coding. |
survey | An individual survey instrument within a project. |
audience | A respondent audience segment deployed against a survey. |
report | A reporting view aggregating data from surveys within a project. |
report_question | An individual question configuration inside a report. |
report_topic | A thematic grouping of questions within a report. |
coding_dictionary | The shared open-end coding scheme for a project's surveys. |
coding_label | An individual code within a coding dictionary. |
translation | A language translation applied to a survey. |
insight | An AI-generated or user-created insight from survey data. |
todo | A task or action item tracked within the platform. |
Actions
Actions describe what a user can do with a resource. Internal actions apply when working in the platform UI. External channel actions control access through the REST API and MCP integrations.
Internal application actions
| Action | Description |
|---|---|
read | View a resource and its details. |
create | Create a new instance of a resource. |
update | Modify an existing resource. |
delete | Permanently remove a resource. |
go_live | Activate a resource, such as launching an audience to begin data collection. |
move | Relocate a resource to a different parent, such as moving a survey between projects. |
export | Export data from a resource. |
update_cache | Refresh cached or computed data for a resource. |
run_internal | Execute an internal platform process associated with a resource. |
External channel actions
| Action | Description |
|---|---|
api_read | Read a resource through the REST API. |
api_run | Execute or trigger operations on a resource through the REST API. |
mcp_read | Read a resource through the MCP integration. |
mcp_run | Execute or trigger operations on a resource through the MCP integration. |
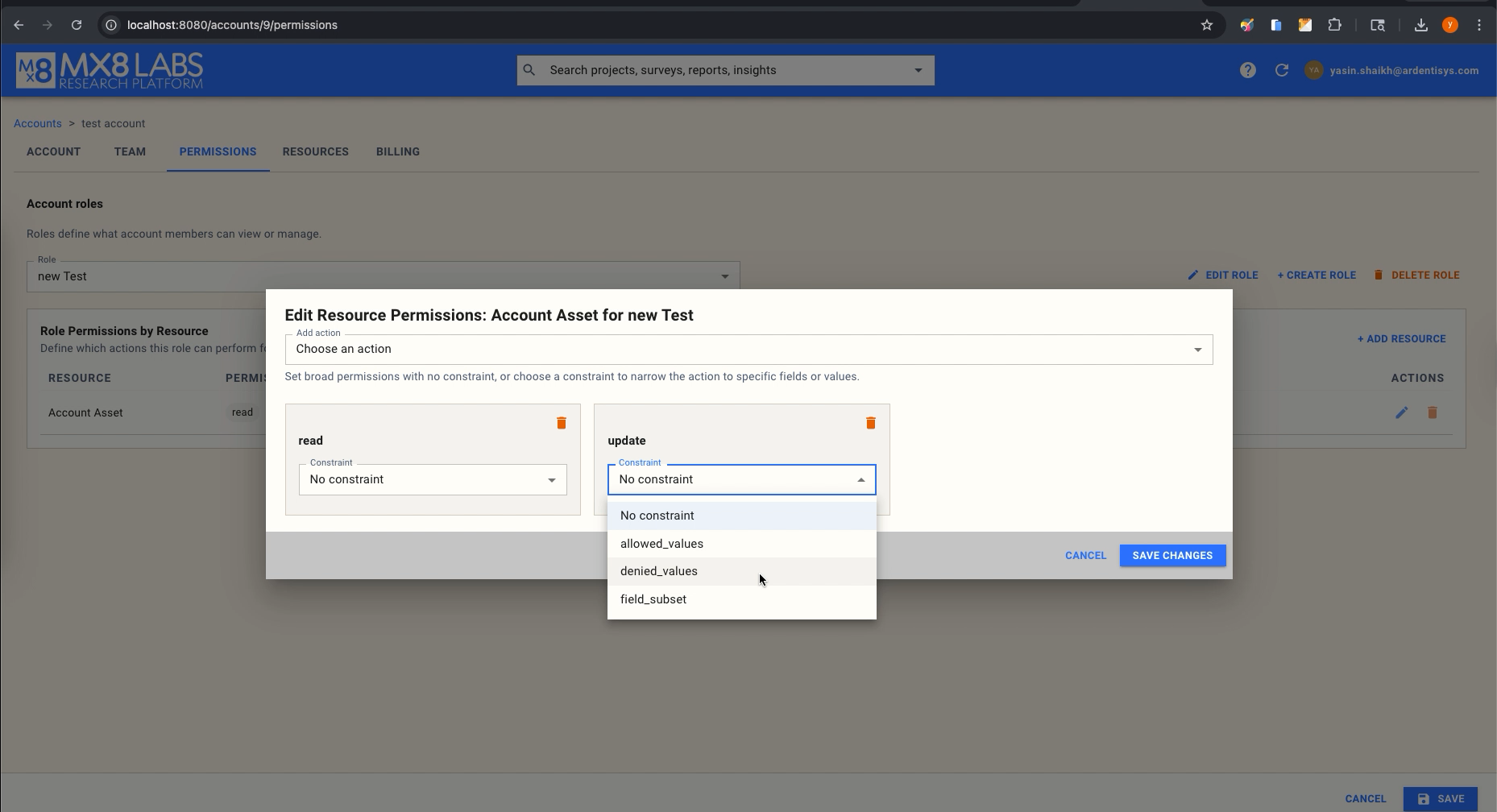
Constraint Types
Constraints narrow a permission to specific fields or values. They are optional — a permission with no constraint grants unrestricted access to the specified action on the resource.
| Constraint Type | Description |
|---|---|
| No constraint | The permission applies without restriction. The user can perform the action on the full resource. |
allowed_values | Restricts a field to a specified list of values. The action is only permitted when the target field's value is in the allowed list. |
denied_values | Blocks a specified list of values for a field. The action is permitted for any value except those in the denied list. Denied values always override allowed values when both apply. |
field_subset | Restricts an update action so the user can only modify the listed fields. Any attempt to change other fields will be denied. |
Constrainable Fields
When attaching a constraint to a permission, you specify which field the constraint applies to. The available fields are:
| Field | Description | Typical Usage |
|---|---|---|
status | The current status of a resource. | Restrict which statuses a role can assign. |
price | The price or cost value on a resource. | Limit which price points a role can set. |
account_id | The owning account identifier. | Control cross-account resource references. |
report_type | The type classification of a report. | Restrict which report types a role can create or modify. |
allow_synthetic | Whether synthetic respondents are permitted. | Prevent or require synthetic respondent usage. |
survey_id | The associated survey identifier. | Scope permissions to specific survey associations. |
project_id | The associated project identifier. | Scope permissions to specific project associations. |
type | The general type classifier on a resource. | Restrict which subtypes a role can work with (for example, audience types). |
name | The display name of a resource. | Limit rename access or restrict to specific naming patterns. |
is_live | Whether a resource is currently live/active. | Prevent a role from changing live status directly. |
System Role: account_member
The account_member role is assigned by default to every user added to an account. It provides read access to all resources and the ability to perform standard research tasks. The table below shows every permission granted.
| Resource | Actions |
|---|---|
All Resources (*) | read |
| Project | create, update |
| Survey | create, update, delete, api_read, api_run, mcp_read, mcp_run |
| Audience | create, update, delete, api_run, mcp_run |
| Report | create, update, delete |
| Report Question | update, delete |
| Report Topic | create, update |
| Coding Dictionary | update |
| Coding Label | create, update, delete |
| Translation | update |
| Insight | create, update, delete |
| Todo | create, update, delete |
Notable exclusions for account_member: no access to modify the account itself, no account asset management, no exposure source management, no go_live permission, no move permission, no export or cache management, and no project deletion.
System Role: account_admin
The account_admin role is assigned to the account creator and includes all member permissions plus elevated administrative access. The table below shows every permission granted.
| Resource | Actions |
|---|---|
All Resources (*) | read |
| Account | update, delete |
| Account Asset | create, update, delete |
| Exposure Source | create, update, delete |
| Project | create, update, delete, move |
| Survey | create, update, delete, move, api_read, api_run, mcp_read, mcp_run |
| Audience | create, update, delete, go_live, api_run, mcp_run |
| Report | create, update, delete |
| Report Question | update, delete |
| Report Topic | create, update |
| Coding Dictionary | update |
| Coding Label | create, update, delete |
| Translation | update |
| Insight | create, update, delete |
| Todo | create, update, delete |
Key additions over account_member: account update and delete, account asset management, exposure source management, project deletion and move, survey move, and audience go_live.
Permission Resolution Rules
When a user holds multiple roles, permissions are resolved using these rules in order:
- Additive coarse permissions — If any role grants an action on a resource, the user has it.
- Additive field grants — Field-level update grants from different roles are merged together.
- Denied values override allowed values — If any role denies a value, it is denied regardless of other roles allowing it.
- Immutable fields win — Certain fields are protected at the platform level and cannot be changed by any role.